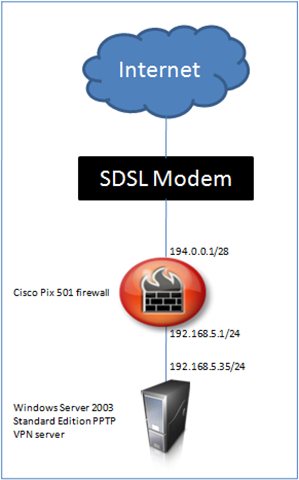
In the following example I am configuring port forwarding to a Windows Server 2003 PPTP VPN server. My lab has been configured as shown in the diagram. I have a /28 network registered on the Internet and 14 public IP Addresses are available though the ISP uplink. The SDSL modem is providing these IP addresses by the internal DHCP server. For the Cisco PIX 501 firewall I am using manual assigned Public IP Address.
How to configure PPTP VPN server publishing on a Cisco PIX 501 firewall?
In the CLI command below I am configuring static NAT to a public IP Address for tcp port 1723 (pptp). I am also allowing the tcp and gre traffic to the VPN server by using access-list.
fixup protocol pptp 1723 name 192.168.5.35 VPN-02 pdm location VPN-02 255.255.255.255 inside static (inside,outside) tcp 194.0.0.2 pptp VPN-02 pptp netmask 255.255.255.255 0 0 access-list outside_access_in permit tcp any host 194.0.0.2 access-list outside_access_in permit gre any host 194.0.0.2
What did I achieve with this configuration?
After I applied this configuration I was able to connect from my Windows XP & Windows Vista computers by utilizing the built-in VPN client via the PPTP protocol. I configured static port forwarding on tcp 1723 port and enabled the GRE IP protocol fix by using the “fixup protocol pptp 1723” command. Without the fixup for pptp protocol I am forced to translate complete internal host (VPN-02) and using all TCP ports. If you don’t apply to fixup than you probably will get eventlog message like one below.
Event Type: Warning Event Source: Rasman Event Category: None Event ID: 20209 Date: 3/18/2008 Time: 9:22:43 PM User: N/A Computer: VPN-02 Description: A connection between the VPN server and the VPN client 87.0.0.1 has been established, but the VPN connection cannot be completed. The most common cause for this is that a firewall or router between the VPN server and the VPN client is not configured to allow Generic Routing Encapsulation (GRE) packets (protocol 47). Verify that the firewalls and routers between your VPN server and the Internet allow GRE packets. Make sure the firewalls and routers on the user's network are also configured to allow GRE packets. If the problem persists, have the user contact the Internet service provider (ISP) to determine whether the ISP might be blocking GRE packets.







Guillermo
I’ve an cisco px 501 (PIX Version 6.3(3)), using the cisco vpn client and works fine from win XP, but the new laptop comes with Vista Business and here cisco vpn client doesn’t work.
Do you know if Vista need some change in config or so on,
Thanks in advance.
Guillermo.
Ivan Versluis
Hi Guillermo, which version of Cisco VPN client did you install? I had problems before and you should install Cisco VPN Client v5 for Vista.
What kind of error message do you get if any?
Send me an email at ivan1980(at)networknet.nl.
Sammy
Thank, the “fixup protocol pptp 1723″ command fixed all my problems
Po LAM
Dear Sir
I have 2 x Cisco Pix 501 with ver 6.3 (5) router, I want to setup Site-to-Site VPN for linkup both internal network. I had found some example configuration from web but still failure.
Could you help me ?
The detail is as follows:
Site 1 have 192.168.6.x have true IP 203.186.x.x with Win2003 server (192.168.6.88)
Site 2 have 192.168.123.x have true IP 223.255.x.x (user need to access the windows server at Site1)
Also, could you tell me why some PC can’t open the PDM but server can ? It due to IE security or Java version ?
Thanks a million
Po
ugg australia boots uk
Great content! I’m all for this. The article is generally helpful for me. Reading your article tends to make me satisfied. At one time, I will be able to learn far more knowledge. Thanks quite definitely.